Have there been any assessments of the vulnerability/resistance of Peplink devices to AirSnitch attacks?
Hi…
At this moment… Using client isolation is the only option.
To prevent malicious Wi-Fi clients from attacking other clients on the same network, vendors have introduced client isolation, a combination of mechanisms that block direct communication between clients. However, client isolation is not a standardized feature, making its security guarantees unclear.
I’m also very interested in this question. Here is the research paper itself: https://www.ndss-symposium.org/wp-content/uploads/2026-f1282-paper.pdf
From the paper:
“Improving Network Isolation. To improve isolation mechanisms on single APs, untrusted BSSIDs (e.g., guest networks) can be put in isolation groups, i.e., VLANs. VLANs logically separate network segments, meaning an attacker on one VLAN cannot send packets to or snoop on another VLAN. This prevents a client in the untrusted BSSID from launching the port stealing attack to redirect traffic destined to the victim in a trusted BSSID. In addition, one could even put each user within (the equivalent of) a unique VLAN, which would securely synchronize the client’s authenticated identity across the network stack; however, the implementation challenges of such a method will need to be investigated. For example, doing so will likely require software updates on most home routers and access points since we find that only a few of the AP devices we analyzed seem to support VLANs out of the box. We have verified via experiments that TP-Link EAP613 can put guest SSIDs into separate VLANs, which effectively nullifies the exploitation techniques listed in Table VI.”
At one of my locations, we have a Balance 20X configured as follows:
- Network
- Network: GuestVLAN
- VLAN ID: 2
- Inter-VLAN routing: [off] (checkbox not selected)
- AP
- GuestSSID
- VLAN: GuestVLAN
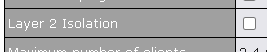
- Layer 2 Isolation: [on] (checkbox selected)
- Guest Protection: Block All Private IP: [on] (checkbox selected)
- GuestSSID
The User Manual says the following about Layer 2 Isolation: “When this option is enabled, clients on the same VLAN, SSID, or subnet are isolated to that VLAN, SSID, or subnet, which can enhance security. Traffic is passed to upper communication layer(s).”
To what extent, if any, would that configuration effectively prevent the AirSnitch attack from being carried out (1) from the GuestSSID against devices connected to other trusted SSIDs, and (2) from the GuestSSID against other devices connected to the GuestSSID?
from the paper it appears that layer 2 isolation can be ineffective in this scenario.
Second, we observe that many vendors only enforce client
isolation at Layer-2 (MAC and link), but do not carry it over
to Layer-3 (IP layer). Thus, we find that an attacker can inject
packets to a victim, by using the AP’s gateway MAC address
as the layer 2 destination, but the victim’s IP address as the
layer 3 destination. These packets are typically accepted by
the AP and forwarded to the gateway. I
Right. I’m hoping Peplink can provide confirmation whether this vulnerability applies to Peplink routers/APs, or whether Peplink does carry over Layer-2 isolation to the IP layer.
Hi All, our team has been working on it and the fixes seem promising. We target to include the fixes in the next GA firmware (tentatively called firmware 8.6.0 for router series, and firmware 3.9.8 for AP series), estimated to be available next few weeks.
More information will be shared when the firmware goes into beta, in coming weeks. Stay tuned.
Hello @WeiMing
What models of the WAPs will receive updates? There are many previous generations of Peplink/Pepwave WAPs still in active service that have not received any updates/patches for over 2 years.
Thanks, Marcus ![]()
I should mention we share the concern @mldowling presents. Indeed, we have more of the earlier versions out there than the current production models. We’d hope Peplink will furnish FW for all AP models – possibly accepting the really old first generation.