I am running several servers which were having weird performance problems. I was finally able to debug the problem by running this command on macOS:
netstat -anp tcp | grep '\.443 '
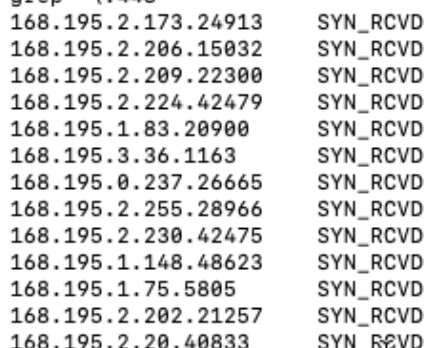
which showed hundreds of tcp4 connections stuck in the “SYN_RCVD” state:
These happen to be Brazilian IP addresses, and we have no customers outside the USA.
Clear evidence of a SYN FLOOD attack.
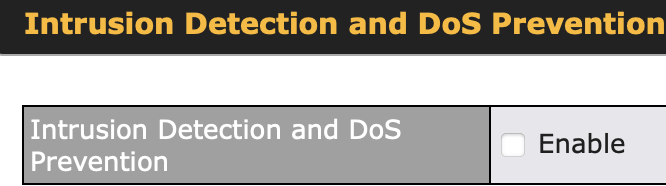
I checked the Peplink UI and found this:
So I enabled it, and applied changes.
The UI states:
When this option is enabled, the unit will be protected by detecting the following types of intrusion and denial-of-service attack.
Port Scan
NMAP FIN/URG/PSH
Xmas Tree
Another Xmas Tree
Null Scan
SYN/RST
SYN/FIN
SYN Flood Prevention
Ping Flood Attack Prevention
However, it had absolutely zero effect.
Does this feature work at all? I could not see any evidence it does anything.
In any case, I was able to ban that IP range which solved the problem for now, but I’d really like to know if the SYN Flood Prevention works.
This is on a Balance One with latest firmware 8.5.4