Please be patient with me. This may be a little long winded, but, the history of this has an impact.
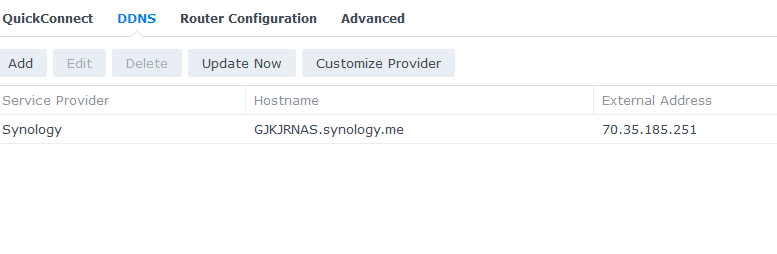
Several years ago my son & I installed Synology NAS devices in our stick & bricks home to facilitate offsite backup as well as using the devices as a WebDav server. In order to map specific folders on the NAS to a drive on a given PC, we use the WebDrive application. At the time we were both using TW cable internet which is now Spectrum. Setup was relatively straight forward & we secured Lets Encrypt SSL certificates as outlined on the Synology application with out incident.
Fast forward to May, 2020. I have become a full time RV’er & installed a Max Transit CAT-18 for my internet connectivity. The mapping of folders on the NAS devices to a drive on a given still functions, however, my scheduled NAS to NAS backups are failing.
Coincidentally, the CISCO router at my son’s home office failed at that time & it was replaced with a Balance One Core. A PepVPN Speed Fusion one to one connection was established with the help of a member of this forum. The backups continue without issue.
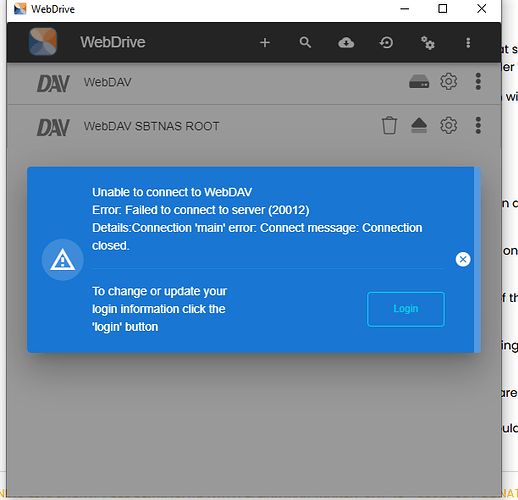
Sometime late last year, Synology released a more secure version of their Disk Management System (DSM). Not a practicing early adopter of anything new, improved & more secure, the update was not applied until last week. While the DSM update went rather smoothly at my son’s location with a cable internet service provider, the WebDav server & WebDrive client application to my NAS failed.
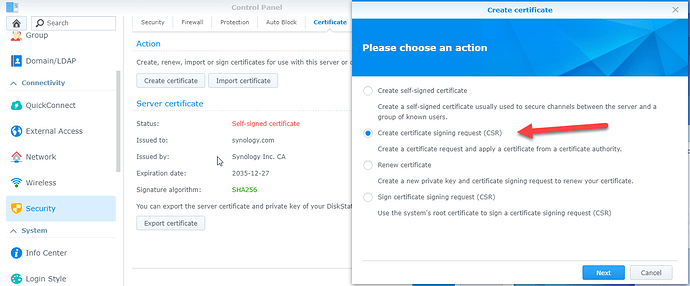
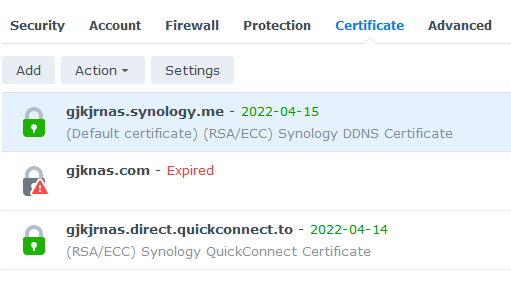
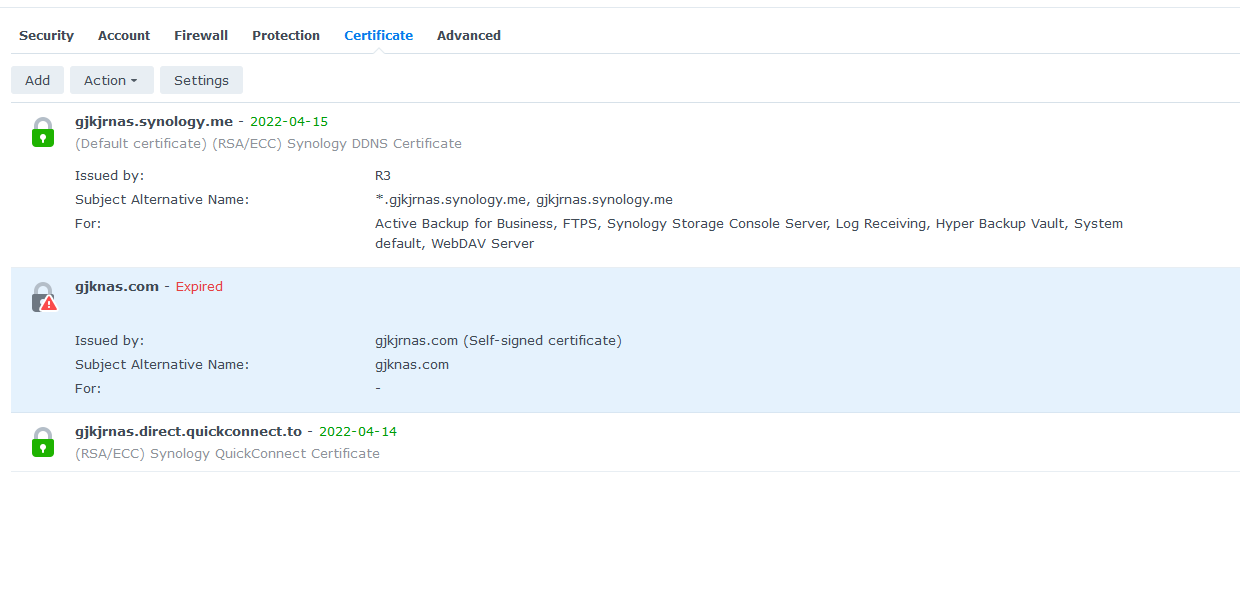
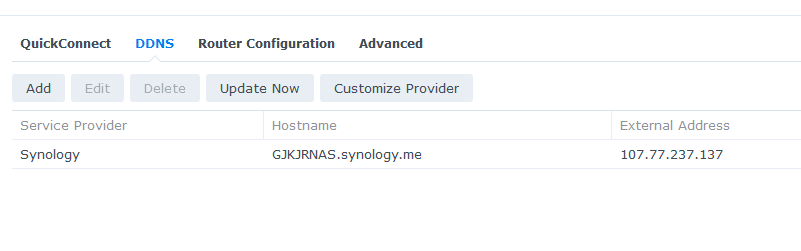
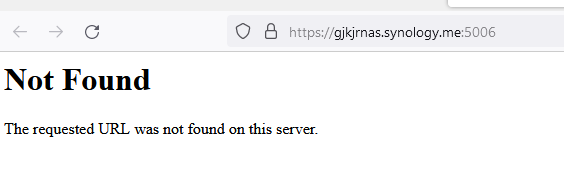
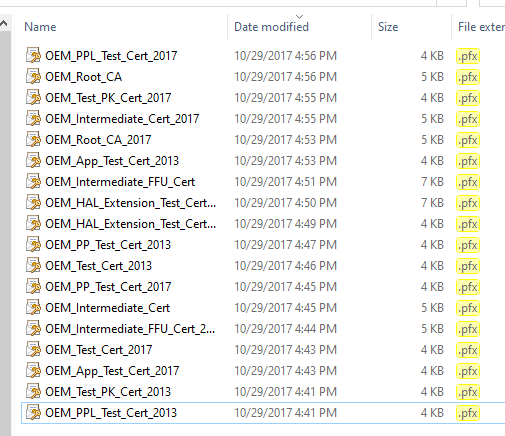
Working with both Synology & WebDrive support, it appears that I no longer have a valid SSL certificate for my NAS. Tech support at Synology at least understands the issues with CGNAT & tell me they are looking for a work around.
Attempts to obtain a new SSL certificate via Let Encrypt times out indicating ports are messed up, check configuration, etc. etc. When I use ‘what is my IP’, it returns 174.247.7.142 which is clearly a Verizon domain. I can not successfully ping this address.
OK, here come the questions:
- Both the Balance One Core & the Max Transit CAT-18 are no longer covered by PrimeCare.
- While the PepVPN SpeedFusion tunnel continues to work, is it because I don’t need PrimeCare or has Peplink just overlooked
that I’m using it? - Can I set up additional tunnels with the PepVPN SpeedFusion, or am I limited to only one?
- Is there a better solution?
- If the solution is to activate PrimeCare, on one or both units, who do I contact as they were purchased from different
suppliers? Will Peplink even allow this? - On the surface, it seems an easy work around would be to take the NAS & my PC to a hardwired connection so Lets Encrypt can send the files that way. By the way, I tried obtaining the SSL certificate via WIFI as WAN with the RV park WIFI just to see if it might work. It did not. Is this the best solution as it’s a 2 hour round trip?
I suspect some iteration involving a SpeedFusion license would solve the problem, but, the folks at the home office don’t deal well with any change which involves the way they do things. I’m not opposed to spending money, but,
Please do not suggest anything involving InControl.
Thanks in advance for any help or suggestions.