I have tried setting firewall rules on the Internal network to isolate specific static IP and/or MAC addresses from other LAN clients, but I am still able to ping the fire-walled devices. I have tried setting them up as source and then as destination, but nothing stops the traffic.
What am I doing wrong?
Are the ips you are denying access to on a different subnet than the IPs that are trying to access them?
Perhaps share an example?
The clients are all on the same subnet. I am using my previous routers as wireless access points. I am using the guest network for my IOT devices. I have the option to allow guest to see each other. That option is is turned off and it works to prevent those devices from seeing each other, but the can still see my local network devices.
That’s why I tried setting firewall rules on the Internal network to isolate those specific static IP and/or MAC addresses from other LAN clients, but I am still able to ping the fire-walled devices.
The firewall is not denying access to the internal network devices.
Could the access points still be allowing this to happen?
Thanks, Dave
Hey
Not sure your use case etc. - just thought I would throw this out there…
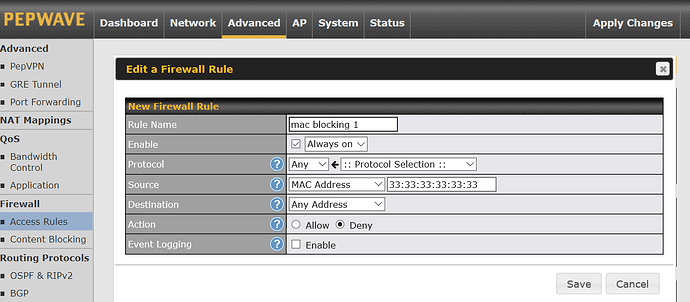
You made this type of internal firewall rule to block the IoT device from talking to other devices…
So that covers one IoT device → all other devices.
But then conversely you would have to do the same thing for each of the other devices on the subnet to prevent them from being able to ping the IoT device. That’s potentially a lot of rules!
If you did all that and it didn’t work then maybe its the old router - if its consumer grade I would suspect it not routing correctly TBH. You could try swapping in another “old router” perhaps?
An alternate solution (more secure) is to VLAN/isolate IoT on the old wireless router / no firewall rules required - but then you would need another wireless router for non IoT assuming your pepwave product doesn’t have one built in.
Addendum:
For example I don’t think a firewall rule on the pepwave would be able to over rule two wireless devices on the old router from pinging each other (ie from the main WiFi to the Guest WiFi), since all that routing occurs on the old router - assuming the old router is malfunctioning / bad firmware / consumer grade etc…
Or…
Bridge mode on the old router may have bridged the main WiFi to the Guest WiFi etc… You could take it off bridge mode?
You have given me some very good ideas about what could be wrong with my setup.
This was my test device which is a smart plug;
I will have to dig a little deeper into this problem.
My set up is very complex, but with your input I should be able to figure it out.
Thanks very much for your expert advice.
No, it won’t. Firewall works between subnets. Two devices on the same subnet can talk directly to each other - they don’t have to go via the router to communicate so the firewall can’t have an effect.
wifi client isolation works because it is performed at an access point level (the AP acts as a wifi networking ‘switch’ and effectively puts all clients into their own VLAN).
Put your guest wifi clients into their own VLAN, then block that VLAN from accessing your other LAN clients.
That’s unfortunate as I was hoping to be able to use my existing equipment.
Due to the topology of my network I am going to need some managed switches to trunk the VLAN’s to each location. The other option is to buy new AP’s that will work with VLAN’s.
At least during this process I am learning new things about networking. ![]()
Thanks for your input,
Dave