I am trying to set up a VLAN and not having any success. I have gone through the manual a number of times and it does not help. I have not been able to find a solution on these forums either. Rather than trying to describe every single thing I have tried (as it is obviously wrong) please let me explain what I am trying to do and what I thought the basic steps were and perhaps someone can offer some advice.
I have a peplink balance one with the newest 6.1.2 firmware (which says it supports VLANs) and want to be able to segment devices on the LAN (ex: computers on one, printers on another, cameras on a third). I would like all VLANs to be able to access the internet and for now I am fine with all vlans communicating with each other but I would also like to know if there is a way to restrict inter vlan routing to specific hosts or one-way in the future (so one machine could access any machine anywhere but not vice versa - I have looked in the firewall settings for that but it all seems to apply to incoming and outgoing connections only not intra-lan ones but perhaps I’m just confused - but anyways my pressing issue is getting the VLAN set up for partitioning)
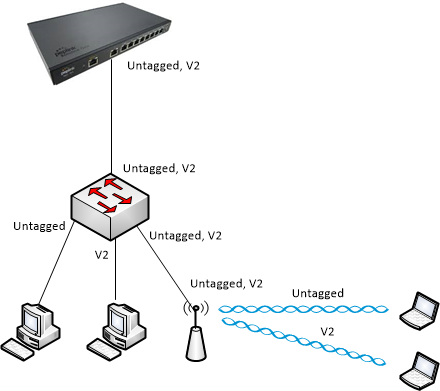
Here is what I am trying so far just as a proof of concept.
MODEM -> BALANCE ONE (192.168.4.1) -> Computer 1 (192.168.4.2xx as assigned by DHCP)
-> Computer 2 (192.168.6.100 - static, gateway 192.168.6.1)
I enabled VLANS per the manual.
Primary:
192.168…4.1 /24
inter vlan routing, checked
dhcp server on
Second:
192.168.6.1 /24
IVR checked
dhcp server on
Doing this, I can connect to the router from the DHCP assigned address in 192.168.4.x on both 192.168.4.1 and 192.168.6.1 but not the static machine on 192.168.6.100.
The second machine to the cannot ping 192.168.6.1 at all (or 4.1).
I looked all over but I can’t see that VLANs are assigned to a specific port on the router so I assume any port on the router should be able to use any VLAN I create? But this is not working.
One other question - I see I can create wireless SSIDs and associate them with a VLAN but aside from that how can have a machine take advantage of the DHCP server on the 192.168.6.x subnet from a wired connection? With no hard-port association I am at a loss.
I really appreciate any help anyone is able to give me - I have spent hours trying to fix this (and searching the internet for answers) but am so far out of luck.